GIVING POWER TO THE EDGE: HOW TO IMPROVE IOT PERFORMANCE AND KEEP SECURITY
- Dec 3, 2021
- 5 min read
CNIT (Consorzio Nazionale Interuniversitario per le Telecomunicazioni), ITALY
Prof. Francesca Cuomo, Prof. Ioannis Chatzigiannakis, Prof. Ilenia Tinnirello, Ph.D Domenico Garlisi, Mr. Pietro Spadaccino.
IoT connectivity and challenges
Low-Power Wide-Area Network (LPWAN) technologies deliver scalable and long-term networks of devices that integrate sensing, computation and wireless communication that are embedded in complex physical indoor and outdoor environments. LPWAN technologies allow embedded devices to communicate directly to network gateways over distances in the range of several kilometres. Today, about 92% of the globally deployed LPWAN are based on one of the following four technologies: LoRaWAN, Sigfox, NB-IoT and LTE-M. IoT Analytics forecast [1] indicates these four flavours of LPWAN as the fastest growing IoT connectivity technologies over the next few years.
In this post, we focus on LoRaWAN [2], an LPWAN technology developed by the LoRa Alliance as an open standard that can operate over private and-or public infrastructures at a global scale. It defines a basic architecture that involves IoT devices (named End-Devices, ED) transmitting their data towards Network Gateways (GW). LoRaWAN networks are based on a highly centralized architecture, according to which all data collected by IoT devices and all decisions about network configuration are managed by a single Network Server (NS). On one hand, the centralized approach helps decouple the network infrastructure from the cloud-based applications that rely on messages arriving from the IoT devices. On the other hand, numerous challenges arise like system scalability, stability, and a lack of proper monitoring and supervision for configuration operation and maintenance.
The ELEGANT paradigm for Edge-Computing
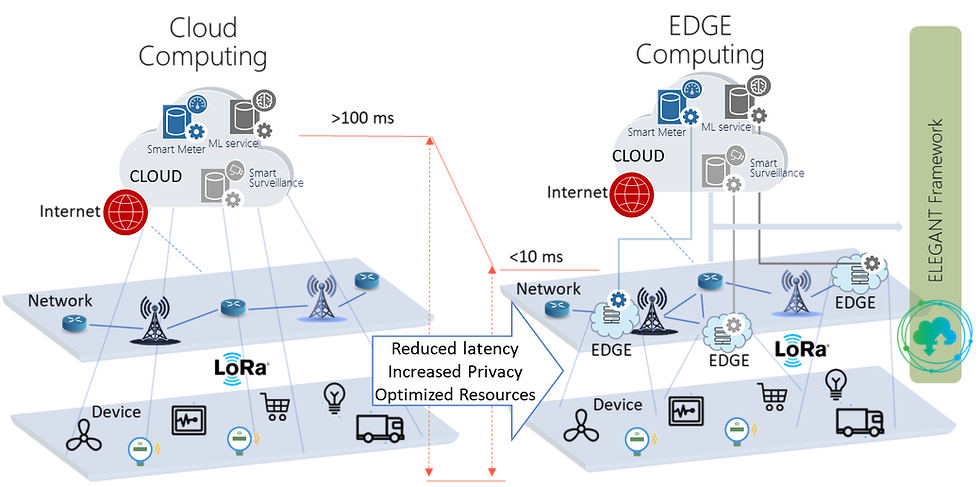
The ELEGANT paradigm bridges the gap between the Cloud and Edge Computing ecosystems by providing a unified, secure and seamless computational and programming environment for IoT/Big-data applications. ELEGANT builds upon a stream-based processing architecture that enables network optimization operations as well as Big Data analytics applications that are deployed at cloud level, to be transparently executed at the edges of the network.
Figure 1 (left side) depicts the operation of LoRaWAN deployments where all packets are transferred to the cloud for centralized processing. The right side of Figure 1 indicates how the network is restructured based on the ELEGANT paradigm, optimizing overall performance in terms of latency, privacy, security and IoT resource usage.
Wireless spectrum optimization using ELEGANT
LoRaWAN supports multi-rate by exploiting six different Spreading Factors (SFs), from 7 to 12, which enable suitable modulations on the radio spectrum [3]. The selection of the data rate is a trade-off between communication range and time-on-air (ToA). LoRaWAN allows EDs to individually select the SF employing an Adaptive Data Rate (ADR) scheme. Alternatively, the NS is also allowed to coordinate the data rates due to its central role. The NS needs to monitor the operation of the network by inspecting the packets received from all the EDs in the network, with a clear impact on the overall scalability of the network.
Following the ELEGANT paradigm, the execution of the EXPLoRa-C ADR algorithm [4] is distributed across the edges of the network. Each distributed instance of the EXPLoRa-C ADR algorithm optimizes the network resources of a given subnet by equally balancing the total offered load spent on each SF. EXPLoRa-C implements the load balance and diversity criteria in terms of ``sequential water-filling''. For facilitating the selection of a data rate compatible with the link budget, EDs are ordered according to their Received Signal Strength Indicator (RSSI) value from the closest GW (from the highest to the lowest value). SF allocations are performed sequentially by verifying: i) the link margin from the candidate SF, ii) the satisfaction of the diverse optimization criteria, iii) and the constraint on the maximum number of EDs on each SF. Decisions are taken at NS and in multiple steps, in which EDs are sequentially processed and allocated to a given SF or moved to a next decision step.
Figure 2 (left side), shows the EXPLoRa-C ADR algorithm’s flow and how each phase is assigned to different Edge resources. The NS groups the network information such that the complete network map of the network is built. In the sequel, the NS divides the network map into the available Edge resources. The performance of the distributed approach is shown in Figure 2 (right side), parallel computation reduces the execution time especially when the EDs number increases. As a result, the ELEGANT-based distributed ADR algorithm improves the IoT system scalability.

Reinforcing Privacy and Network Security using ELEGANT
LPWAN networks are used for delivering smart metering services. Information collected from ED and delivered to the smart services is sensitive and needs to be protected since (a) the ED are deployed in potentially remote locations, (b) packets need to travel across long distances to reach a GW, (c) the infrastructure is designed for long-time operation, spanning more than 15 years [6]. Regardless of the way communication is protected using network and application-level encryption, there are still several weaknesses connected with device identification that may lead to the disclosure of sensitive information, with a direct impact on the privacy of the end-users [5].
Following the ELEGANT paradigm, distributed de-anonymization can be leveraged by the network operator to enhance network security and improve the privacy of data while at the same time performing network optimization [5]. Figure 3 depicts how certain functionalities implemented within the network server can be transferred to the edges of the network to perform de-anonymization. Each distributed instance of the de-anonymization algorithm produces unique device identifiers for the corresponding subnet assigned.

Smart water monitoring using ELEGANT
Water metering, a major challenge for most cities around the world, is achieved by collecting data from many thousands of water meters using either on-site visits or manual drive-by methods. The main obstacles to the digitisation of this process are the number of water meters and their operational lifetime requirements, making the use of technologies like 4/5G-based connectivity highly inefficient and inappropriate. Following the ELEGANT paradigm, a hierarchical data-processing architecture is introduced using multiple layers of LoRaWAN, Wireless-MBus and 4/5G mobile networks and edge computing to increase the data collection rates, prolong the lifetime of the whole infrastructure, minimise the additional cost while increasing the benefits, and enabling the data-driven extraction of useful conclusions like consumption profiling or incident detection [7]. A stream-based water consumption profiling algorithm is deployed to each edge resource to identify common patterns in water consumption across buildings within the same subnet. The spatial relationship between the buildings is propagated within the hierarchical data-processing architecture to identify patterns of usage between buildings across subnets [8].
Reference
[1] Global LPWAN market forecast by vertical. IoT Analytics. LPWAN Market Report 2018-2023. https://iot-analytics.com/product/lpwan-market-report-2018-023/, September 2018
[2] LoRa Alliance Technical Committee. LoRaWAN 1.1 Specification. https://lora-alliance.org/resource-hub/lorawantm-specification-v11, 2017.
[3] Semtech. LoRa. EP2763321 from 2013 and U.S. Patent 7,791,415 from 2008, 2015.
[4] D. Garlisi, I. Tinnirello, G. Bianchi, and F. Cuomo. Capture aware sequential waterfilling for lorawan adaptive data rate. IEEE Transactions on Wireless Communications, PP:1–1, 12 2020. https://doi.org/10.1109/TWC.2020.3038638.





Comments